Simple, secure, and effective
Airlock enables you to easily create and manage secure allowlists (formerly application whitelists) in dynamically changing computing environments.
Workflow Based Allowlisting


Simple Deployment, Operation and Maintenance
Until now, Allowlisting (commonly referred to as Application Control or Application Whitelisting) has been difficult to deploy and maintain within an organisation. Airlock has been developed from the ground up by security professionals to solve real world problems with Allowlisting.
Airlock incorporates proven and effective workflows, designed for ease of use in dynamically changing enterprise environments. Allowlisting with Airlock is a simple, repeatable process.
Realtime Reporting, Detection and Response
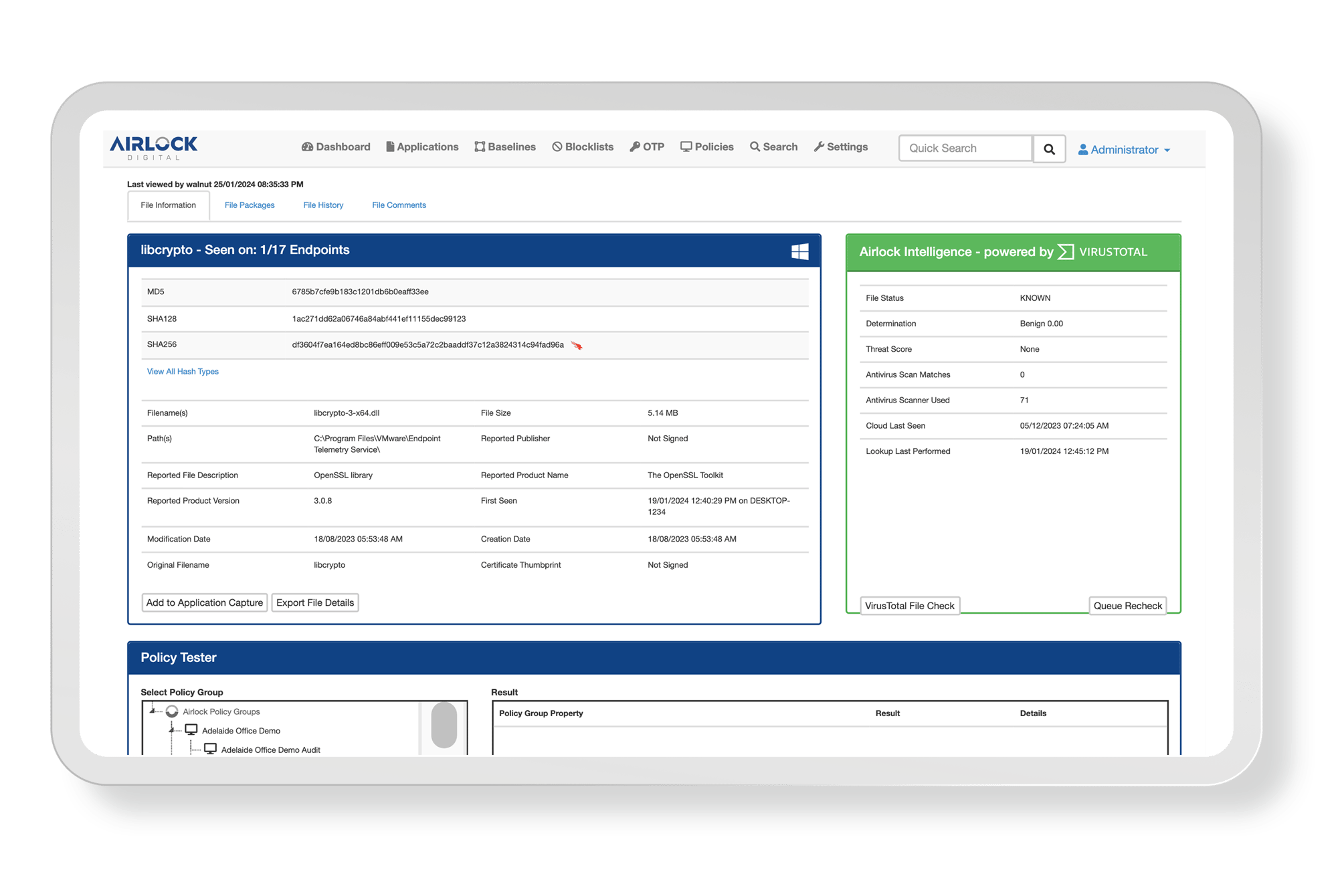
Airlock provides centralised visibility over all files within in an organisation. Discover when a file was first seen in your environment, where it came from and how it was executed.
Files can be centrally queried, perfect for security operations teams.

Lightweight
Many security offerings typically rely on large endpoint agents and the delivery of bulky virus definitions to function. Often these definitions can be upwards of two hundred megabytes in size for each endpoint.
The Airlock Enforcement Agent is lean, with small policy sizes and minimal impact on endpoint resources across Windows, Linux and macOS. Trust definitions are strictly within control of the administrator, with no regular agent definitions provided by a third party, this also enables the solution to operate entirely without an internet connection if required.
Prevent Ransomware and targeted Cyber Intrusions
Modern attacks involve the modification of files, or the creation of unique malware to avoid detection by traditional security software. “99% of malware hashes are seen for only 58 seconds or less. In fact, most malware was seen only once. This reflects how quickly hackers are modifying their code to avoid detection.”1
As each customer makes decisions regarding what files they trust in-house, each deployment is unique. This prevents cyber-criminals from testing their attacks or modifying their code to avoid detection


Meet Security Compliance
Watch a Product Demonstration Now
Fill in your contact details to access the product demonstration video.